Free Resources
Thanks for Trusting Us - Download In one Click
Nmap - Hidden Commands
A practical, command-based guide to using Nmap beyond basic port scanning. This PDF focuses on real-world reconnaissance techniques.

Amass – Subdomain Enumeration Basics
Beginner-friendly guides to understanding subdomain enumeration using Amass. Learn how assets are discovered, mapped, and organized during reconnaissance.
PDF • Infographics • Mind Maps

Blue Teaming Fundamentals
Learn the basics of defensive security. These resources explain how blue teams monitor, detect, and respond to cyber threats in real-world environments.
PDF • Infographics • Mind Maps

Burp Suite for Beginners
Step-by-step beginner guides to Burp Suite. Understand proxying, request analysis, and basic web testing concepts without getting overwhelmed.
PDF • Infographics • Mind Maps

Cybersecurity Basics Guide
A complete beginner introduction to cybersecurity concepts, terminology, attack types, and defense strategies explained in a simple and visual way.
PDF • Infographics • Mind Maps

Default Passwords Awareness
Understand why default credentials are dangerous. Learn common misconfigurations, real-world risks, and how attackers exploit weak passwords.
PDF • Infographics • Mind Maps
FFUF
Beginner-friendly resources explaining directory and parameter fuzzing using FFUF. Learn how fuzzing helps uncover hidden endpoints and assets.
PDF • Infographics • Mind Maps

Nmap – Network Scanning Basics
Learn how Nmap is used to discover live hosts, open ports, and running services. These beginner resources explain scanning concepts in a simple and visual way.
PDF • Infographics • Mind Maps
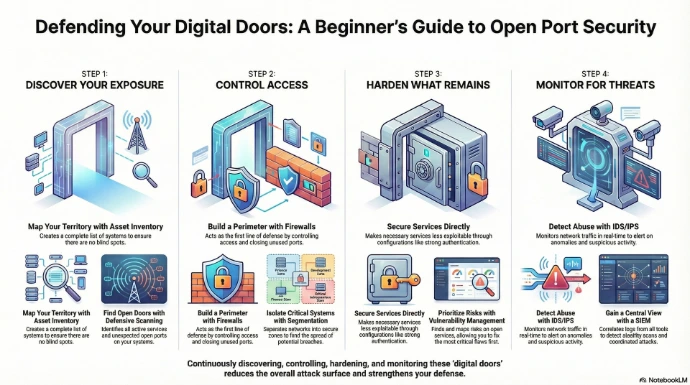
Open Ports Explained
Understand what open ports are, why they matter in cybersecurity, and how attackers identify exposed services during reconnaissance.
PDF • Infographics • Mind Maps

Phishing Attacks – Beginner Guide
Learn how phishing attacks work, common techniques used by attackers, and how users and organizations can identify and prevent them.
PDF • Infographics • Mind Maps
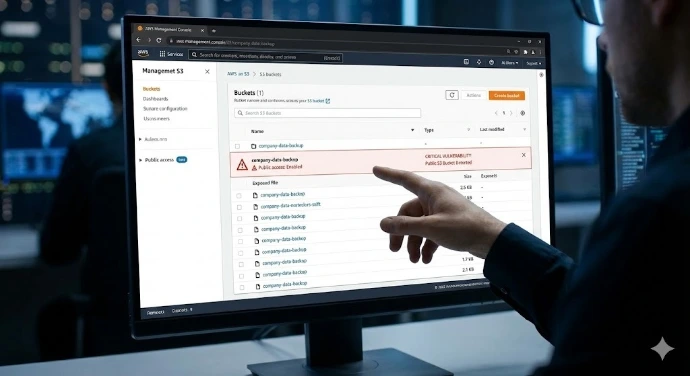
Public S3 Bucket Misconfigurations
Beginner-friendly guides explaining what public S3 buckets are, why misconfigurations happen, and how exposed cloud storage leads to data leaks.
PDF • Infographics • Mind Maps

Red Teaming Fundamentals
An introduction to offensive security and red team operations. Learn how simulated attacks help organizations test and improve their defenses.
PDF • Infographics • Mind Maps
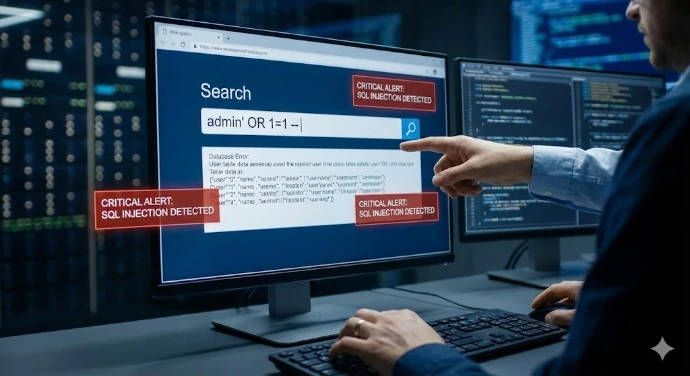
SQL Injection for Beginners
Learn the fundamentals of SQL injection, how input flaws are exploited, and how developers can prevent database-level attacks.
PDF • Infographics • Mind Maps

Cross-Site Scripting (XSS) Basics
Beginner resources explaining XSS attacks, how malicious scripts are injected, and how proper validation and encoding prevent them.
PDF • Infographics • Mind Maps

Zero-Day Vulnerabilities Explained
Learn what zero-day vulnerabilities are, why they are dangerous, and how attackers exploit unknown flaws before patches are available.
PDF • Infographics • Mind Maps
Web Cache Deception Explained
Learn how web cache deception works, why sensitive data gets cached accidentally, and how improper caching rules can expose private information.
PDF • Infographics • Mind Maps

Web LLM Security Basics
An introduction to Large Language Model (LLM) security in web applications. Learn common risks, misuse scenarios, and basic protection concepts.
PDF • Infographics • Mind Maps
Open Redirect Vulnerability
Learn what open redirect vulnerabilities are, how attackers abuse them for phishing and attacks, and how applications can prevent unsafe redirects.
PDF • Infographics • Mind Maps

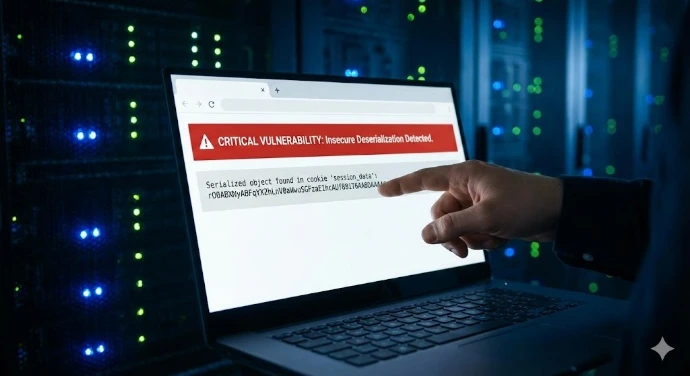
Cryptographic Failures Explained
Beginner-friendly explanation of cryptographic failures, weak encryption, poor key management, and how these mistakes expose sensitive data.
PDF • Infographics • Mind Maps
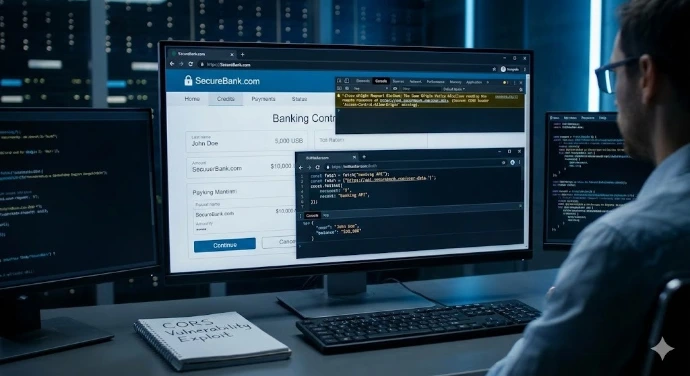
CORS Explained Simply
Understand Cross-Origin Resource Sharing (CORS), why browsers enforce it, common misconfigurations, and how CORS issues impact web security.
PDF • Infographics • Mind Maps

CIA Triad – Security Fundamentals
Learn the core principles of cybersecurity: Confidentiality, Integrity, and Availability. A must-know foundation for every security learner.
PDF • Infographics • Mind Maps
