1️⃣ Introduction — Why Authentication is a Prime Target

Authentication is the front gate of every digital system. Whether it’s a banking app, SaaS platform, corporate VPN, or social media account — the login mechanism is the first security barrier standing between an attacker and sensitive data.
From an offensive security perspective, breaking authentication is often far more valuable than exploiting deeper infrastructure vulnerabilities. Why? Because if you can log in as a legitimate user — or worse, an administrator — you inherit all their privileges without triggering many traditional security alarms.
🔐 Authentication = The First Security Barrier
Every secure workflow begins with identity verification:
Username & password
Multi-Factor Authentication (MFA)
Biometrics
OAuth / SSO tokens
Session cookies
If this layer is implemented correctly, it stops unauthorized access at the door. But if it’s flawed, attackers don’t need malware, exploits, or zero-days — they simply walk in through the front entrance.
Hackers target authentication because it provides the shortest path to impact.
🚨 If Login Breaks → Full Account Takeover
An authentication bypass vulnerability can immediately lead to Account Takeover (ATO) — one of the most critical security failures in any application.
Once attackers gain access, they can:
Impersonate victims
Access private communications
Extract stored credentials
Abuse business logic
Escalate privileges
And unlike many technical exploits, authentication abuse often looks like normal user behavior, making detection harder.
💥 Real-World Impact of Authentication Failures
When login systems fail, the consequences go far beyond unauthorized access.
Common real-world impacts include:
Data Theft
Exposure of PII, health records, source code, or confidential business data.
Financial Fraud
Unauthorized transactions, wallet withdrawals, reward point abuse.
Administrative Access
Attackers gaining control over dashboards, user databases, or infrastructure controls.
In bug bounty programs, authentication bypass vulnerabilities are frequently classified as P1 / Critical severity due to their direct business impact.
🛡️ OWASP Top 10 — Broken Authentication
Authentication risks are so prevalent that they’ve consistently appeared in the
OWASP Top 10 under categories like:
Broken Authentication (A2:2017)
Identification & Authentication Failures (A7:2021)
This classification highlights systemic issues such as:
Weak credential handling
Session mismanagement
MFA implementation flaws
Logic bypass vulnerabilities
For offensive security professionals, OWASP serves as both a testing roadmap and a bug hunting goldmine.
📊 Breach Statistics & Industry Reality
Multiple cybersecurity reports over the years have shown a consistent trend:
A significant percentage of breaches involve compromised credentials.
Stolen or bypassed authentication remains one of the top initial attack vectors.
Account takeover attacks continue to rise across fintech, SaaS, and cloud platforms.
This isn’t just because passwords are weak — it’s because authentication systems themselves are often flawed.
⚠️ Why Modern Apps Still Fail
Despite advances in security tooling, authentication bypass vulnerabilities remain widespread.
The reason?
Most auth flaws are logic-based, not technology-based.
Modern applications use strong frameworks, encryption, and identity providers — yet they still fail due to:
Improper validation flows
Trusting client-side controls
Broken MFA enforcement
Insecure API authentication
Misconfigured tokens or sessions
Hackers don’t break encryption — they break implementation mistakes.
🧠 Attacker Mindset
To an offensive security tester, every login page raises key questions:
Can I skip authentication entirely?
Can I manipulate the request?
Can I impersonate another user?
Can I abuse session handling?
Can I break MFA logic?
Because sometimes, you don’t need a password…
You just need a flaw in how it’s checked.
⚠️ Disclaimer:
This content is published strictly for educational and ethical cybersecurity research purposes. All techniques discussed are intended to help security professionals identify and remediate vulnerabilities. Do not attempt testing on systems without proper authorization.
2️⃣ Understanding Authentication Mechanisms

Before attempting to bypass authentication, an offensive security professional must first understand how login systems actually work behind the scenes. Exploitation rarely comes from breaking cryptography — it comes from abusing flawed implementations, misconfigurations, or broken logic flows.
Purpose: Hackers exploit implementation mistakes, not theory.
Let’s break down the core authentication mechanisms used in modern applications and where weaknesses typically emerge.
🔑 Session-Based Authentication
This is the traditional authentication model used by many web applications.
How it works:
User submits username & password.
Server validates credentials.
Server creates a session stored on the backend.
A session ID is sent to the browser (usually via cookies).
Every subsequent request includes this session ID.
Security Weak Points:
Predictable session IDs
Session fixation
Session IDs exposed in URLs
No session expiration
Session reuse after logout
If an attacker steals or sets a valid session ID, they can log in without credentials.
🪙 Token-Based Authentication (JWT)
Modern applications, especially SPAs and APIs, use JSON Web Tokens (JWT) instead of server sessions.
How it works:
User logs in.
Server issues a signed JWT.
Token is stored client-side (localStorage / cookies).
Token is sent with each request (Authorization header).
JWT contains:
User ID
Roles/permissions
Expiry time
Signature
Security Weak Points:
Weak signing secrets
alg=none misconfigurations
Token tampering
Long expiry tokens
Accepting expired tokens
Attackers analyze tokens to forge or manipulate identities.
🌐 OAuth / SSO Logins
OAuth enables login via third parties like Google, Microsoft, or GitHub.
Flow Simplified:
User chooses “Login with Google.”
App redirects to provider.
Provider authenticates user.
App receives an authorization token.
Security Weak Points:
Improper token validation
Email trust without verification
Account linking flaws
Redirect URI misconfigurations
OAuth bypasses often lead to account takeover without passwords.
📲 MFA / OTP Authentication
Multi-Factor Authentication adds a second verification layer:
SMS OTP
Email OTP
Authenticator apps
Push approvals
Flow:
User enters password.
Server requests OTP.
User submits OTP.
Access granted.
Security Weak Points:
OTP reuse
No rate limiting
Predictable OTPs
Bypassing OTP step via API
Response manipulation
Improper MFA implementation gives a false sense of security.
🍪 Cookies & Session IDs
Cookies store authentication state in browsers.
Common auth cookies:
Session ID
Remember-me tokens
JWT tokens
Security Flags That Matter:
HttpOnly
Secure
SameSite
Security Weak Points:
Missing flags
Cookie theft via XSS
Transmission over HTTP
Persistent login abuse
Cookie compromise often equals instant authentication bypass.
🧠 Key Takeaway
Each authentication mechanism is secure by design — but only if implemented correctly.
Attackers don’t attack the protocol…
They attack:
Validation logic
Token handling
Session management
Flow enforcement
Understanding these systems is what enables precise bypass exploitation.
3️⃣ Authentication Attack Surface Mapping

Before attempting any login bypass, skilled hackers perform attack surface mapping — identifying every entry point where authentication logic exists.
Because authentication isn’t limited to just the login page.
Every workflow that verifies identity becomes a potential attack vector.
🎯 Why Attack Surface Mapping Matters
Many critical auth bypasses are found outside the main login form, including:
APIs
Mobile apps
Recovery flows
Secondary verification steps
If you only test the visible login panel, you’ll miss high-impact vulnerabilities.
🔎 Key Areas Hackers Test
Below are the primary authentication entry points offensive testers map and probe:
1️⃣ Login Panel
The obvious starting point.
Tests include:
SQL injection
Default credentials
Parameter tampering
Logic flaws
Rate limit bypass
2️⃣ Registration Functionality
New account creation can expose auth flaws.
Test cases:
Creating accounts without verification
Role manipulation during signup
Email validation bypass
Duplicate account logic
3️⃣ Password Reset Flow
Often weaker than login security.
Common tests:
Token prediction
Reset link reuse
Email parameter tampering
IDOR in reset requests
Password reset = alternate login path.
4️⃣ OTP Verification Systems
Critical MFA attack surface.
Tests include:
Brute forcing OTP
Skipping OTP step
Manipulating verification responses
Testing expired OTP acceptance
5️⃣ Remember-Me Functionality
Persistent login features introduce risk.
Potential flaws:
Long-lived tokens
Reusable cookies
Token leakage
Device binding failures
6️⃣ API Login Endpoints
Modern apps rely heavily on APIs.
Why APIs matter:
Often lack frontend protections
May skip validation layers
Easier to fuzz & automate
Tests:
Direct login requests
Token issuance flaws
MFA bypass via API
7️⃣ Mobile App Authentication APIs
Mobile apps frequently expose hidden endpoints.
Why they’re valuable:
Hardcoded tokens
Debug endpoints
Weak certificate pinning
Alternate auth flows
Testing mobile APIs often reveals vulnerabilities not present in web apps.
🧠 Pro Tip Section
Always test APIs even if UI is secure.
Many organizations heavily secure their web login interfaces but neglect backend APIs powering:
Mobile apps
Partner integrations
Internal dashboards
Attackers target these overlooked pathways to bypass authentication entirely.
4️⃣ Core Authentication Bypass Techniques
This is the heart of authentication exploitation — where theory turns into real offensive tradecraft.
Authentication bypass rarely relies on a single flaw. Instead, attackers analyze requests, logic flows, tokens, and verification layers to identify weaknesses that allow access without valid credentials.
Let’s break down the most impactful techniques used in real-world pentests and bug bounty engagements.
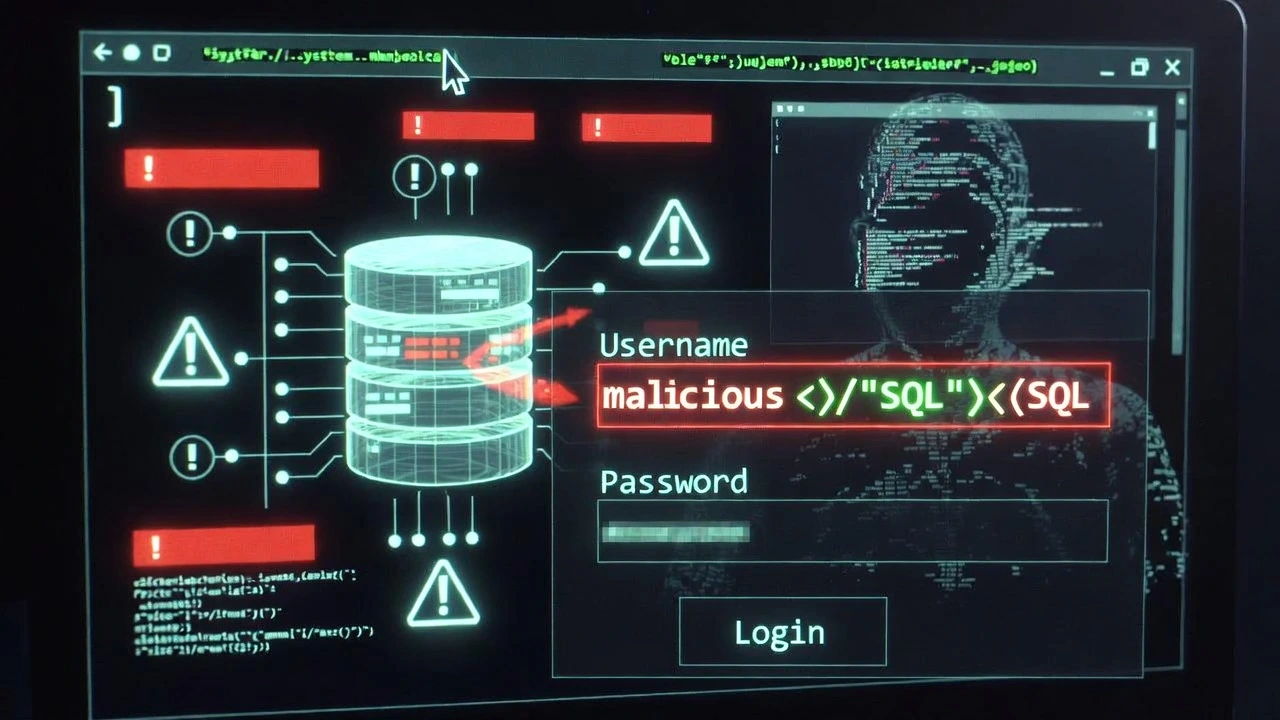
4.1 SQL Injection Login Bypass
🔎 Concept
SQL Injection (SQLi) in authentication occurs when user input is unsafely embedded into backend database queries.
Instead of validating credentials, the database is tricked into returning a true condition — granting access.
🧠 Authentication Query Structure
A typical login query looks like:
SELECT * FROM users WHERE username='USER' AND password='PASS';
If inputs aren’t sanitized, attackers can manipulate query logic.
⚡ Classic Payload Logic
By injecting SQL operators, attackers alter authentication conditions.
Example logic:
Force query to always return TRUE
Comment out password checks
Inject alternate conditions
This results in login success without knowing credentials.
✅ Boolean-Based Bypass
Boolean injections manipulate TRUE/FALSE logic:
TRUE condition → login granted
FALSE condition → login denied
Attackers craft inputs that guarantee a TRUE outcome.
🧩 Knowledge Add-Ons
Modern Filters & WAF Bypass
Even when filters exist, attackers evade them using:
Encoding techniques
Case manipulation
Inline comments
Alternate operators
Blind SQLi in Login
If no visible error/output exists, attackers rely on:
Response timing
Login success/failure differences
Conditional payload testing
Blind SQLi can still yield full authentication bypass or credential extraction.
4.2 Default & Hardcoded Credentials
🔎 Concept
Many systems ship with preconfigured credentials for setup, testing, or maintenance — and they’re often left unchanged.
Attackers test these first because they require zero exploitation effort.
🔑 Common Examples
admin : admin
admin : password
test : test
root : root
Vendor-specific defaults
🎯 High-Value Targets
IoT & Network Panels
Routers
CCTV systems
Smart devices
CMS Dashboards
WordPress
Joomla
Drupal staging panels
Development Environments
QA servers
Staging apps
Debug dashboards
Hardcoded credentials may also exist inside:
Mobile apps
JavaScript files
API configurations
4.3 Parameter Manipulation
🔎 Concept
Authentication decisions often rely on backend parameters — not just username/password.
If attackers can modify these values, they may escalate privileges or bypass verification.
🛠️ Techniques
Intercept login requests (proxy tools)
Modify POST/JSON parameters
Change hidden form fields
Replay altered requests
💥 Example Exploitation Angles
Privilege Escalation
role=user → role=admin
Verification Bypass
is_verified=false → true
Account State Manipulation
account_status=pending → active
If the server trusts client-supplied values, authentication enforcement collapses.
4.4 Authentication Logic Flaws
🔎 Concept
Logic flaws are among the most valuable findings in bug bounty because they bypass security without technical exploits.
They arise from broken workflows rather than code injection.
🧠 Common Cases
1. Login Without Password Validation
Backend validates username existence but skips password checks under certain conditions.
2. Skipping Verification Steps
Attackers directly access post-login endpoints without completing authentication.
3. Accepting Blank Passwords
Improper validation allows empty or null password submissions.
4. Client-Side Only Password Checks
Password verification happens in JavaScript — easily bypassed by intercepting requests.
💎 Why Logic Bugs Matter
Harder to detect automatically
Often overlooked in pentests
Lead to full account takeover
High bounty payouts
4.5 OTP / MFA Bypass Techniques
🔎 Concept
Multi-Factor Authentication is meant to stop unauthorized logins — but flawed implementations create new attack vectors.
⚡ Common OTP/MFA Bypass Methods
OTP Reuse
Previously used OTPs remain valid.
Missing Rate Limits
Unlimited OTP attempts enable brute force.
Predictable OTPs
Weak randomization or sequential codes.
Response Manipulation
Altering server responses:
"otp_verified": false → true
Direct API Access
Attackers skip OTP UI and directly access authenticated APIs.
🧠 Real-World Insight
Many organizations implement MFA for compliance — not security — leading to exploitable logic gaps.
4.6 Session Fixation & Session Hijacking
🔎 Concept
If authentication is tied to session IDs, controlling or stealing sessions equals controlling accounts.
🧷 Session Fixation
Attacker sets a known session ID before login:
Victim logs in.
Session remains unchanged.
Attacker reuses session to access account.
🕵️ Session Hijacking
Stealing valid session tokens via:
XSS attacks
Network sniffing
Malware
Browser leaks
🍪 Cookie Security Weaknesses
Insecure Flags
Missing:
HttpOnly
Secure
SameSite
Transport Leakage
Session cookies sent over HTTP can be intercepted via MITM attacks.
Result → Login without credentials.
4.7 JWT & Token Misconfigurations
🔎 Concept
Token-based authentication shifts trust to signed tokens — but misconfigurations enable forgery.
⚠️ Common JWT Attacks
alg=none Attack
Server accepts unsigned tokens.
Weak Signing Secrets
Attackers brute-force signing keys to forge tokens.
Token Tampering
Modifying payload data:
"user_role": "user" → "admin"
If signature validation fails, privilege escalation occurs.
Expired Token Acceptance
Improper validation allows reuse of expired tokens.
🧠 Why JWT Bugs Are Critical
Because tokens often contain:
User identity
Roles
Permissions
Email
Account IDs
Forging one token can equal full system compromise.
4.8 Password Reset Bypass
🔎 Concept
Password reset functions act as alternative authentication systems — often with weaker security controls.
Attackers target resets because they’re easier to exploit than login forms.
🔓 Common Exploitation Techniques
Token Prediction
Weak or sequential reset tokens.
Email Parameter Manipulation
Altering reset request emails to receive victim reset links.
Reset Link Reuse
Tokens remain valid after password change.
IDOR in Reset Flow
Changing user identifiers to reset other accounts’ passwords.
💥 Impact
Password reset bypass can lead to:
Instant account takeover
Privilege escalation
Admin compromise
All without touching the login page.
🧠 Section Takeaway
Authentication bypass isn’t a single vulnerability class — it’s an ecosystem of flaws across:
Databases
Sessions
Tokens
APIs
Logic workflows
Verification systems
Elite offensive testers don’t just test passwords…
They test every trust decision an application makes.
5️⃣ Real-World Case Study Section

To truly understand the impact of authentication bypass vulnerabilities, it helps to examine how they unfold in real environments. Case studies not only add credibility but also demonstrate attacker mindset, methodology, and business impact.
Below is a realistic, high-value offensive security case study structured the way bug bounty reports and pentest findings are documented.
🏦 Target Type
Fintech Web Application (Digital Wallet Platform)
A bug bounty hunter was testing a fintech platform that allowed users to:
Store funds
Transfer money
View KYC data
Access transaction history
Given the financial nature, authentication and MFA protections were expected to be robust.
🔍 Vulnerability Found
OTP Authentication Bypass via API Logic Flaw
While the web login enforced OTP verification, the backend API responsible for session issuance did not properly validate OTP completion state.
In short:
The system generated authenticated sessions before OTP verification was finalized.
🛠️ Exploitation Steps (High Level)
1️⃣ Researcher intercepted login requests using a proxy.
2️⃣ Observed two API calls:
/login → Validated username & password
/verify-otp → Completed MFA
3️⃣ After password validation, the server issued a temporary authenticated token.
4️⃣ Researcher replayed this token directly against protected endpoints:
/account/details
/wallet/balance
5️⃣ APIs responded successfully — even though OTP was never verified.
6️⃣ By automating this request flow, the researcher achieved full login bypass.
💥 Impact Achieved
The vulnerability allowed attackers to:
Bypass MFA completely
Access user wallets
View transaction history
Extract KYC documents
Initiate fund transfers (with additional flaws chained)
This effectively reduced a 2-factor authentication system to single-factor security.
💰 Bounty Earned / Severity
Severity: Critical (P1)
Bounty Awarded: $12,000
CWE Mapping: Improper Authentication
OWASP Category: Identification & Authentication Failures
The report was additionally recognized in the company’s security hall of fame due to the financial risk involved.
🧠 Key Lessons from This Case
MFA implementations often fail in backend APIs.
Session issuance timing is critical.
Always test authentication flows beyond the UI.
Chaining auth flaws can multiply impact.
6️⃣ Tools Hackers Use for Auth Bypass
Authentication bypass testing requires more than manual trial-and-error. Offensive security professionals rely on specialized tools to intercept, manipulate, replay, and automate authentication workflows.
Below is a practical toolkit used in real bug bounty and pentesting engagements.
🧰 1️⃣ Burp Suite (Proxy + Repeater)
Primary Use: Intercepting and modifying authentication requests.
🔍 How It Helps
Capture login POST requests
Modify parameters (username, password, roles)
Test SQLi payloads
Manipulate OTP verification responses
Replay altered requests
Repeater Module
Allows attackers to:
Manually tweak requests
Test bypass payloads
Observe response differences
Burp acts as the central testing hub for auth bypass research.
🎯 2️⃣ Intruder (Bruteforce / Fuzzing)
A Burp Suite module used for automation.
🔍 How It Helps
Brute force OTP codes
Test default credentials
Fuzz login parameters
Discover hidden auth fields
Identify rate-limit flaws
Attack Types Used:
Sniper
Cluster Bomb
Pitchfork
Intruder accelerates discovery of authentication weaknesses at scale.
🗄️ 3️⃣ SQLmap
Primary Use: Automated SQL Injection exploitation.
🔍 How It Helps
Detect SQLi in login forms
Automate payload injection
Bypass authentication via DB manipulation
Extract user credential databases
SQLmap is especially useful when manual SQLi testing confirms injection points.
🪪 4️⃣ JWT.io
Primary Use: JWT analysis and manipulation.
🔍 How It Helps
Decode JWT tokens
Inspect payload data
Identify roles/permissions
Test signature validation
Attempt token tampering
Researchers use it to:
Modify claims
Test weak secrets
Validate signing algorithms
JWT misconfigurations often lead to privilege escalation.
📡 5️⃣ Postman
Primary Use: API authentication testing.
🔍 How It Helps
Send direct login API requests
Replay intercepted tokens
Test OTP verification endpoints
Automate auth workflows
Bypass frontend validation layers
Postman is ideal for testing headless authentication flows outside the browser.
🚀 6️⃣ FFUF / wfuzz
Primary Use: Endpoint fuzzing & parameter discovery.
🔍 How They Help
Discover hidden auth endpoints
Fuzz login parameters
Identify alternate verification APIs
Bruteforce reset tokens
Enumerate authentication paths
Particularly powerful for:
API-heavy apps
Microservices environments
Mobile backend testing
🧠 Toolchain Strategy
Elite hackers rarely rely on one tool.
A typical workflow might look like:
Intercept login → Burp Proxy
Manipulate requests → Repeater
Automate fuzzing → Intruder / FFUF
Exploit SQLi → SQLmap
Analyze tokens → JWT.io
Test APIs → Postman
Tool chaining dramatically increases bypass discovery success.
7️⃣ Step-by-Step Testing Methodology
Authentication bypass testing becomes far more effective when approached through a structured offensive methodology rather than random payload testing.
Below is an actionable, field-tested workflow used in bug bounty and penetration testing engagements.
🪤 Step 1 — Intercept Login Request
Start by capturing the authentication request using an intercepting proxy.
Objectives:
Observe request method (POST/JSON/XML)
Identify parameters
Capture headers, cookies, tokens
What to look for:
Username & password fields
Hidden parameters
MFA flags
Session identifiers
This intercepted request becomes your base attack template.
🔬 Step 2 — Analyze Parameters
Once captured, dissect the request structure.
Focus Areas:
Parameter names & values
Role identifiers
Verification flags
Account states
Ask:
Are extra parameters trusted?
Is validation server-side?
Are any values user-controlled?
Hidden or unused parameters often lead to privilege escalation or bypass.
💉 Step 3 — Test SQL Injection Payloads
Next, probe input fields for injection vulnerabilities.
Testing Strategy:
Inject boolean conditions
Test authentication logic manipulation
Observe login success/failure patterns
Indicators of SQLi:
Authentication bypass
Error messages
Response delays
Different HTTP status codes
Even blind injection can enable login bypass or credential extraction.
🧩 Step 4 — Modify Responses
Authentication isn’t only about requests — responses matter too.
Techniques:
Intercept server responses
Modify verification flags
Force success states
Example Angles:
"authenticated": false → true
"otp_verified": false → true
If the frontend trusts manipulated responses, authentication enforcement collapses.
🚀 Step 5 — Fuzz Authentication APIs
Modern authentication relies heavily on APIs.
Use fuzzing tools to:
Discover hidden endpoints
Test alternate login paths
Identify undocumented parameters
Targets:
/api/login
/auth/verify
/session/create
/mfa/validate
APIs often lack the layered protections present in web interfaces.
🧠 Step 6 — Test Logic Flaws
Logic testing is where elite hunters find critical bugs.
Questions to explore:
Can login complete without password validation?
Can OTP steps be skipped?
Can you directly access authenticated endpoints?
Are verification steps enforced server-side?
Test workflows — not just payloads.
🪪 Step 7 — Attempt Token Manipulation
If authentication uses tokens, shift focus to token security.
Testing Areas:
JWT payload tampering
Role escalation
Expiry bypass
Signature validation flaws
Key Goal:
Forge or alter tokens to impersonate higher-privileged users.
🧭 Methodology Recap
Intercept authentication
Map parameters
Test injection flaws
Manipulate responses
Fuzz APIs
Break logic flows
Exploit tokens
Following a structured approach ensures no attack surface is missed.
8️⃣ Common Developer Mistakes

Understanding developer mistakes is critical for offensive testers because most authentication bypasses stem from implementation failures — not design flaws.
This section also strengthens SEO while educating defenders.
❌ Client-Side Validation Reliance
Developers sometimes validate credentials using JavaScript only.
Risk:
Attackers intercept requests
Remove validation logic
Send unauthorized requests directly
Server-side enforcement becomes nonexistent.
❌ Missing Rate Limiting
Without rate limits, attackers can:
Bruteforce passwords
Enumerate usernames
Guess OTP codes
Test reset tokens
Rate limiting is essential for authentication resilience.
❌ Weak Session Handling
Session mismanagement leads to:
Session fixation
Session reuse
No expiry enforcement
Logout not invalidating sessions
Poor session hygiene equals persistent unauthorized access.
❌ Predictable Tokens
Reset tokens, session IDs, or OTPs generated using weak randomness allow attackers to:
Predict valid tokens
Hijack accounts
Reset victim passwords
Secure token generation must use cryptographic randomness.
❌ Improper MFA Enforcement
Common MFA mistakes include:
Issuing sessions before OTP validation
Allowing OTP bypass via APIs
Accepting reused OTPs
Skipping MFA for trusted devices improperly
MFA is only effective if enforced across all authentication paths.
🧠 Developer Mistake Pattern
Most auth flaws stem from:
Trusting client input
Inconsistent backend validation
Broken workflow sequencing
Security added as an afterthought
For hackers, these mistakes are opportunity zones.
9️⃣ Impact of Authentication Bypass

Authentication bypass vulnerabilities are among the most severe findings in offensive security because they undermine the core trust boundary of an application.
Once authentication fails, all downstream security controls become irrelevant.
💥 Account Takeover (ATO)
The most immediate impact.
Attackers gain full control over victim accounts, enabling:
Data access
Activity impersonation
Credential harvesting
Service abuse
ATO is a top priority in bug bounty programs.
👑 Administrative Access
If bypass affects privileged accounts, impact escalates drastically.
Attackers may gain access to:
Admin dashboards
User databases
Financial systems
Infrastructure controls
Admin compromise often leads to platform-wide breaches.
🪪 PII Exposure
Authentication protects sensitive identity data such as:
Government IDs
Addresses
Health records
Contact details
Exposure triggers regulatory violations (GDPR, HIPAA, etc.).
💸 Financial Fraud
In fintech or e-commerce systems, attackers can:
Transfer funds
Abuse wallets
Redeem reward points
Perform unauthorized purchases
Financial impact increases severity classification.
🕸️ Lateral Movement
Once authenticated, attackers pivot deeper into systems by:
Accessing internal APIs
Enumerating users
Escalating privileges
Chaining vulnerabilities
Authentication bypass often becomes the initial foothold in broader attacks.
📊 Severity Mapping
CVSS Scoring Factors
Authentication bypass typically scores high due to:
Low attack complexity
No user interaction
High confidentiality impact
High integrity impact
Many cases fall into CVSS 8.0 – 10.0 (Critical).
🏆 Bug Bounty Severity
| Impact Level | Severity | Priority |
|---|---|---|
| User account takeover | High | P2 |
| MFA bypass | Critical | P1 |
| Admin login bypass | Critical | P1 |
| Token forgery | Critical | P1 |
Severity increases when chained with financial or data exposure risks.
🔟 Prevention & Mitigation (Defensive Angle)

While this is an offensive security guide, including defensive controls strengthens technical authority, improves SEO depth, and aligns with responsible disclosure practices.
Securing authentication requires layered defenses across validation, sessions, tokens, and verification workflows.
🛡️ Strong Server-Side Validation
Authentication decisions must always be enforced on the server.
Best practices:
Never trust client input
Validate credentials backend-only
Enforce verification flags server-side
Block parameter tampering
Client-side validation should enhance UX — not enforce security.
🍪 Secure Session Management
Session security is foundational to authentication integrity.
Key controls:
Regenerate session IDs after login
Enforce session expiration
Invalidate sessions on logout
Bind sessions to IP/device (where feasible)
Secure cookie flags:
HttpOnly
Secure
SameSite
Proper session hygiene prevents fixation and hijacking attacks.
📲 Proper MFA Enforcement
Multi-Factor Authentication must be implemented as a mandatory, server-validated step.
Controls include:
Issue sessions only after OTP verification
Enforce MFA across APIs
Prevent OTP reuse
Implement expiry windows
Bind OTPs to sessions/users
MFA should never be bypassable via alternate endpoints.
⏱️ Rate Limiting & Brute Force Protection
Authentication endpoints must enforce request throttling.
Protect against:
Password bruteforce
OTP guessing
Token enumeration
Credential stuffing
Controls:
Attempt limits
Temporary lockouts
CAPTCHA challenges
Behavioral detection
Rate limiting drastically reduces automated bypass feasibility.
🪪 Secure JWT Signing & Token Handling
For token-based authentication:
Security controls:
Use strong signing algorithms (RS256/ES256)
Protect private keys
Reject alg=none
Enforce token expiry validation
Rotate signing secrets regularly
Never trust unsigned or weakly signed tokens.
🧩 Zero-Trust Authentication Design
Modern security architecture assumes breach — not prevention.
Zero-trust principles:
Verify every request
Enforce least privilege
Continuously validate sessions
Monitor behavioral anomalies
Require step-up authentication for sensitive actions
Authentication becomes continuous, not one-time.
🔐 Defensive Takeaway
Authentication security isn’t a single control — it’s a layered ecosystem spanning:
Identity validation
Session integrity
Token security
Workflow enforcement
Behavioral monitoring
Attackers exploit gaps between these layers.
Defenders must ensure there are none.
1️⃣1️⃣ Checklist for Bug Hunters
When testing authentication mechanisms, having a repeatable checklist ensures you don’t overlook high-impact bypass vectors. Elite bug hunters rely on structured testing rather than ad-hoc payload spraying.
Use this quick, actionable checklist during engagements:
🔎 Login & Credential Testing
☐ Test SQL Injection in login fields
☐ Attempt authentication with blank passwords
☐ Check default & hardcoded credentials
☐ Test username/email enumeration
☐ Try credential stuffing scenarios
🧩 Parameter & Request Manipulation
☐ Intercept login requests via proxy
☐ Modify POST/JSON parameters
☐ Test hidden fields in forms
☐ Attempt role escalation (user → admin)
☐ Alter verification flags (is_verified, active)
📲 MFA / OTP Security
☐ Attempt OTP brute force
☐ Test OTP reuse
☐ Check OTP expiry enforcement
☐ Try bypassing OTP via direct API access
☐ Manipulate OTP verification responses
🔐 Session & Cookie Testing
☐ Inspect session cookie flags
☐ Test session fixation possibilities
☐ Attempt session reuse after logout
☐ Check HTTP vs HTTPS cookie transmission
☐ Attempt session hijacking via token capture
🪪 Token-Based Authentication
☐ Decode and analyze JWT tokens
☐ Attempt role/claim manipulation
☐ Test weak signing secrets
☐ Check alg=none acceptance
☐ Test expired token reuse
🔁 Password Reset & Recovery
☐ Test password reset token predictability
☐ Attempt reset link reuse
☐ Manipulate email parameters
☐ Check IDOR in reset flow
☐ Test account takeover via reset
🚀 API Authentication Surface
☐ Fuzz authentication endpoints
☐ Test alternate login APIs
☐ Bypass MFA via backend APIs
☐ Replay intercepted tokens
☐ Test mobile app auth endpoints
🧠 Pro Hunter Tip
Always test authentication workflows — not just login forms.
Many critical bypasses exist in verification steps, APIs, and recovery flows rather than the primary login panel.
1️⃣2️⃣ Conclusion
Authentication systems are designed to be the strongest defensive layer — yet in offensive security, they often deliver the highest return on investment.
Why?
Because breaking authentication doesn’t just expose a vulnerability…
It grants trusted access.
🎯 Key Takeaways
Authentication flaws = Highest ROI bugs
One bypass can equal full account or admin compromise.
Logic testing > Automation
Tools find injections. Minds find workflow flaws.
Attack surface > Login page
Reset flows, APIs, MFA systems often break first.
Trust boundaries are fragile
Small validation gaps create massive impact.
🧠 Attacker Mindset
Great hackers don’t think like testers checking boxes.
They think in questions:
What does the server trust?
What can I manipulate?
What step can I skip?
What happens if validation fails?
Because authentication security isn’t about passwords…
It’s about trust enforcement.
🚀 Ready to Go Beyond Theory? Start Hacking Authentication in the Real World.
If this guide opened your eyes to how login systems really break — imagine what you’ll uncover with structured labs, real case studies, and guided offensive training.
At Bugitrix, we help ethical hackers and bug hunters turn skills into impact:
🔓 Deep-dive offensive security articles
🧠 Real bug bounty case studies
🛠️ Hands-on exploitation labs
📚 Cybersecurity learning paths
💰 Bug hunting methodologies that pay
🌐 Explore More: https://bugitrix.com
📢 Join Our Telegram Community: https://t.me/bugitrix
Get exclusive content, live discussions, new research drops, and early access to tools & learning resources.
Break authentication. Hunt smarter. Earn bigger — with Bugitrix.