Let me tell you how an attacker thinks.
They're not sitting in a dark room trying to crack some Hollywood-style firewall. They're not writing exotic malware for months. Most of the time? They're just logging in.
With your credentials.
That's the uncomfortable reality of cloud security in 2026. The biggest threat isn't some genius hacker. It's a stolen password, a leaked token, or one employee who clicked the wrong email. And once an attacker gets those — they're inside your cloud environment, walking around like they own the place.
Because technically, the system thinks they do.
First, Let's Understand What "The Cloud" Actually Means

If you're just starting out in cybersecurity, this matters a lot.
When a company uses "the cloud," it means their stuff — emails, databases, files, code, customer data — isn't stored in one physical server room. It's spread across services like Microsoft 365, AWS, Google Cloud, Salesforce, and dozens more.
Each of those services has a login page. Publicly accessible. On the internet. Every single day.
That's the attack surface. Not a building with a guarded entrance. A login page that anyone in the world can reach.
Now you understand why identity is everything.
The Numbers That Should Wake You Up
Identity weaknesses played a material role in almost 90% of cyber investigations in 2025. Initial access was driven by identity-based techniques — phishing, stolen credentials, brute force, and insider activity — in 65% of cases. Cybersecurity Insiders
Read that again. 9 out of 10 major incidents. Identity.
Unit 42 responded to over 750 major cyber incidents across 50+ countries in 2025. In almost 90% of those cases, identity was implicated. And over 90% of those breaches were enabled by preventable gaps — not sophisticated nation-state attacks. GuidePoint Security
That word "preventable" is the one that stings. These weren't unavoidable. They happened because of weak passwords, missing MFA, forgotten accounts, and credentials sitting on the dark web for months before anyone noticed.
How Hackers Actually Do It — Step by Step
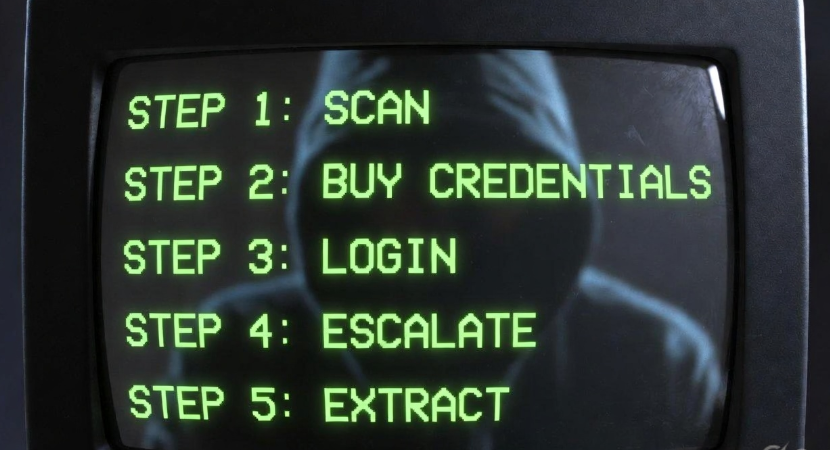
This is what the attacker's playbook looks like. Understanding it is the first step to stopping it.
Step 1: Find a target
Attackers don't always pick a specific company. Many use automated tools to scan the internet for exposed login pages — Microsoft 365 portals, AWS consoles, Salesforce instances. It's like fishing with a net, not a rod.
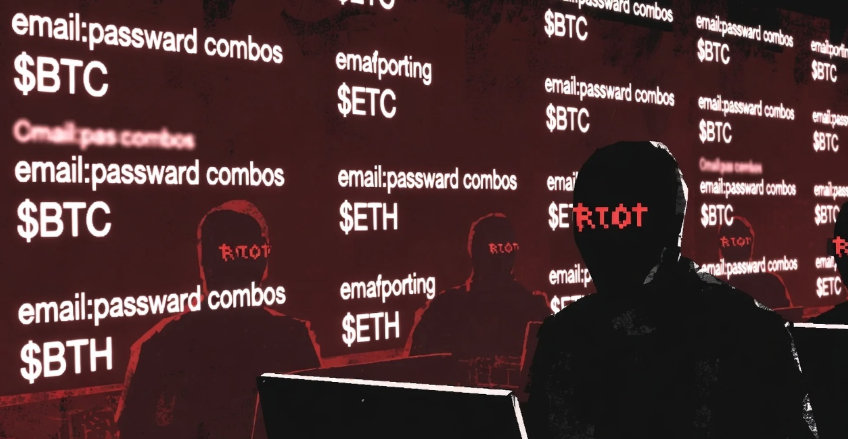
Step 2: Get the credentials
Here's where most people are surprised. Hackers don't crack passwords most of the time. They buy them.
There's an entire underground marketplace where leaked credentials are sold cheaply. Millions of usernames and passwords from old data breaches — from LinkedIn in 2012, Adobe in 2013, various healthcare apps — are still being recycled because people reuse passwords.
Researchers found that browser-based activity was involved in nearly half of all 2025 investigations — routine web browsing can become the starting point for memory-resident malware and credential theft. Cybersecurity Insiders
Step 3: Log in and look around
Once they're in, they don't immediately do damage. Smart attackers spend time exploring. They check what permissions the account has, look for admin access, find connected apps, identify where the sensitive data lives.
This phase is quiet. Invisible. Most organizations don't even know they've been compromised yet.
Step 4: Escalate privileges
If the stolen account is a regular employee, the attacker looks for ways to reach higher — an admin account, a DevOps token, a service account with broad permissions. Among organizations that experienced a cloud breach, "weak identity hygiene" — unrotated keys, unused credentials, orphaned accounts, absence of MFA — turned small slips into major incidents. Dark Reading
Step 5: Extract or destroy
At this point they either quietly steal data over weeks, deploy ransomware, or both. The fastest 25% of intrusions in 2025 reached full data exfiltration in just 72 minutes — compared to 285 minutes in 2024. AI is compressing the entire attack lifecycle. Cybersecurity Insiders
72 minutes. That's less than a lunch break.
Real Breaches. Real Damage. Real Lessons.

Stats are one thing. Real stories hit different. Here's what actually happened in 2025.
Jaguar Land Rover
Hackers accessed JLR's internal files, software source code, and employee login credentials. They reportedly got in through stolen passwords from one of the company's external contractors — a supply chain identity attack that put intellectual property at serious risk. CSO Online
The lesson: your cloud security is only as strong as the weakest vendor you've given access to.
Qantas Airlines
Attackers abused a Salesforce-integrated third-party app to pull CRM data from multiple companies at once. Qantas's own systems weren't directly hacked — but data stored in a cloud service they trusted was compromised. Hackers eventually dumped the data on the dark web. Cymulate
One compromised upstream vendor. Multiple companies hit. This is the cloud's version of a domino effect.
Yale New Haven Health
Hackers were inside their systems for over a month before the breach was reported, exposing the data of 5.56 million people — equivalent to the population of a small U.S. state. Old servers and forgotten accounts that sat unpatched gave attackers their opening. Industrial Cyber
Forgotten accounts. Unpatched servers. These aren't exotic vulnerabilities. They're housekeeping failures.
The Microsoft Entra ID Vulnerability That Shook Cloud Security

If you want to understand how deep the identity problem goes, pay attention to this one.
In 2025, researcher Dirk-jan Mollema discovered a critical vulnerability in Microsoft Entra ID — tracked as CVE-2025-55241 with a perfect CVSS score of 10.0. The flaw involved undocumented internal "Actor Tokens" that Microsoft services use internally, which bypassed Conditional Access, MFA, and standard logging. An attacker could craft a malicious token in their own tenant and use it to gain Global Administrator privileges in virtually any other tenant. SentinelOne
What made this especially alarming was that these tokens didn't generate telemetry in the victim's environment — meaning an attack could have unfolded with almost no traces. SentinelOne
Think about that. Even with MFA turned on, even with logging enabled — an attacker could have walked through the front door of any Azure environment and left no footprints.
Identity providers are the single point of failure in the cloud. This vulnerability proved it at scale.
Why Beginners Miss This (And How to Not Be That Person)
When you're starting out in cybersecurity, it's easy to focus on the exciting stuff — malware analysis, penetration testing, exploits. Identity security sounds boring.
It's not. It's the most critical thing you can learn right now.
Here's why beginners often miss it:
They assume "MFA is enough." It's a great start, but MFA can be bypassed through SIM swapping, phishing-resistant session token theft (AiTM attacks), and social engineering the help desk.
They ignore service accounts and API keys. Every cloud environment has dozens of non-human identities — automated scripts, integrations, tokens. These are often over-privileged, rarely rotated, and completely forgotten. Attackers love them.
They don't think about what happens after a credential is stolen. Most students focus on prevention. Attackers focus on what they can do once they're in.
According to CSA's State of Cloud and AI Security 2025 report, insecure identities and risky permissions are now the number one cloud security risk — above misconfigurations, above malware, above everything else. Dark Reading
What You Should Actually Do About It
Whether you're a student learning security or someone helping protect a small business — here's what matters most.
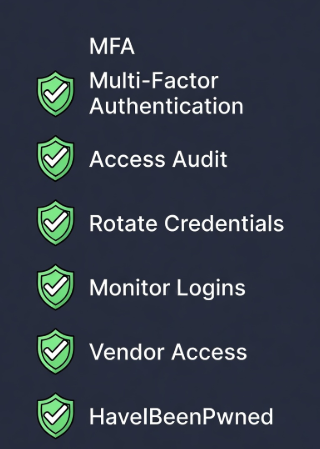
Use phishing-resistant MFA Standard SMS-based MFA is better than nothing but can be bypassed. FIDO2 hardware keys or passkeys are significantly more secure. If you're setting up any cloud environment — start here.
Audit who has access to what Log into your cloud provider and look at every user, service account, and API key. Ask: does this account still need this level of access? Half of them probably shouldn't exist anymore.
Rotate credentials regularly Old keys and credentials sitting around are gifts to attackers. Build a habit of rotating API keys, service account passwords, and admin credentials on a schedule.
Monitor for suspicious logins Enable login alerts. If an account logs in from a new country, at 3am, downloading 50GB of data — that needs to trigger an alarm. Cloud providers have built-in tools for this; most organizations just don't turn them on.
Check your vendor access Every third-party app you've connected to your cloud environment is a potential entry point. Audit them. Remove the ones you don't use. Restrict permissions on the ones you do.
Check HaveIBeenPwned Seriously. Go to haveibeenpwned.com right now and check if your email has appeared in any known breach. It takes 30 seconds and might be the most useful thing you do today.
The AI Problem Making All of This Worse
Just when defenders were starting to catch up, attackers got a new weapon.
Researchers in 2025 observed threat actors using AI to speed up reconnaissance, write more convincing phishing messages, and generate scripts used during ransomware deployment. One simulation showed an AI-assisted attack reaching full data exfiltration in just 25 minutes. Cybersecurity Insiders
APT28, a Russian state-sponsored group, used a new Python-based infostealer that integrated a large language model to dynamically generate commands during runtime — the first publicly documented case of malware using an LLM mid-attack. The Hacker News
The attacker's playbook is evolving fast. Phishing emails that were once obviously fake now read naturally. Attack tools that took hours to configure can now be set up in minutes.
The window to detect and respond is shrinking. Which means the fundamentals — getting identity hygiene right — matter more than ever.
Conclusion: The Door Was Unlocked the Whole Time
Here's the honest truth about most cloud breaches.
They don't happen because someone built an incredible zero-day exploit. They happen because a credential was reused. Because MFA wasn't enforced. Because a vendor account was never deactivated after a contract ended. Because an API key from 2021 was still active and nobody remembered it existed.
The attacker didn't break in. The door was unlocked.
In 2026, the cloud is where everything lives. And identity is the key to everything in the cloud. That makes it the single most important thing to understand, protect, and monitor — whether you're a student just starting out, a developer building apps, or someone trying to protect a business.
The good news? Most of the fixes aren't complicated. They just require attention.
Start there.
🔐 Learn More at Bugitrix

Bugitrix is built for people who are serious about understanding cybersecurity — from the very basics to advanced concepts.
If this article clicked for you, here's where to go next:
💬 Got questions? Join the community. We have real people — students, professionals, researchers — answering questions every day. 👉 bugitrix.com/forum/help-1
📲 Want daily threat intel and tips? Join our Telegram for quick updates, real-world attack breakdowns, and security news that actually matters. 👉 t.me/bugitrix
🌐 Explore more resources: Tutorials, tools, research, and beginner guides — all in one place. 👉 www.bugitrix.com
Knowledge is your first layer of defence. Build it here.