Introduction – So, You Want to Be a Pentester?
Penetration testing is no longer a “cool hacker job” — it’s now one of the most critical roles in modern cybersecurity.
Every company today assumes one thing:
“We will be attacked. The only question is — when?”
And that’s exactly where penetration testers come in.
They are the ethical attackers.
The simulated adversaries.
The professionals paid to break systems before real hackers do.
But here’s the harsh reality most beginners don’t realize…
Getting into penetration testing is not just about knowing tools.
You can complete labs…
You can earn certifications…
You can exploit machines on Hack The Box…
…and still fail interviews badly.
Why?
Because pentest interviews are designed to test something deeper:
Your thinking process
Your attack methodology
Your decision-making under constraints
Your real-world exposure
Your ability to explain risk to businesses
Most candidates prepare the wrong way.
They memorize definitions like:
“What is SQL Injection?”
“What is XSS?”
“What is Nmap?”
But interviewers rarely care about textbook definitions.
Instead, they ask questions like:
“You find a login panel — what’s your testing approach?”
“You got a low-privilege shell — what next?”
“Firewall is blocking ICMP — how will you discover live hosts?”
See the difference?
They’re testing how you think like an attacker, not how you recite like a student.
The Skill Gap Problem
There’s a massive gap in the industry today:
| Candidates Think Interviews Test | Recruiters Actually Test |
|---|---|
| Tool knowledge | Methodology |
| Definitions | Attack logic |
| Certifications | Practical exposure |
| Theory | Decision making |
| Payloads | Risk understanding |
That’s why many CEH-certified candidates fail…
…and self-taught hackers with labs & writeups get hired.
What Makes Pentest Interviews Unique?
Unlike many IT roles, pentesting interviews are:
Practical
Scenario-driven
Discussion-heavy
Lab-oriented
Report-focused
Interviewers want to know:
Can you identify attack surfaces?
Can you chain vulnerabilities?
Can you escalate privileges?
Can you pivot internally?
Can you write a professional report?
Because in real jobs…
Running a scanner ≠ penetration testing.
What This Guide Will Help You With
This blog is built differently from generic interview lists.
You’ll get:
Categorized interview questions
Real-world scenarios
Tool-based discussions
Methodology breakdowns
Recruiter expectations
Practical interview tips
Whether you are:
A beginner preparing for your first pentest role
A bug bounty hunter moving into corporate pentesting
A SOC analyst transitioning to Red Team
A student preparing for cybersecurity placements
…this guide will help you understand how pentest interviews actually work.
How Penetration Tester Interviews Are Structured

One of the biggest mistakes candidates make is preparing blindly — without understanding the interview structure.
Pentesting interviews are rarely single-round.
They are designed to evaluate you from multiple angles:
Technical depth
Practical skills
Communication ability
Reporting mindset
Ethical judgment
Let’s break down how most companies structure their pentester hiring process.
🧭 Round 1 – HR / Screening Round
This is usually the first filter.
It may feel non-technical, but it sets the tone.
What They Evaluate
Communication skills
Passion for cybersecurity
Career motivation
Cultural fit
Salary expectations
Common Questions
Why penetration testing?
How did you get into cybersecurity?
What labs or platforms do you practice on?
What certifications do you hold?
Are you comfortable with legal/ethical boundaries?
They’re checking whether you’re genuinely interested…
…or just chasing a “hacker” title.
🧪 Round 2 – Technical Interview
This is where real evaluation begins.
Depending on the role level, questions may cover:
Core Areas Tested
Networking fundamentals
Web application security
System exploitation
Linux & Windows basics
Common vulnerabilities
Tools & frameworks
But remember…
They don’t just ask definitions.
They test depth.
Example
Instead of asking:
“What is SQL Injection?”
They’ll ask:
How do you manually test SQLi?
How do you bypass WAF?
How do you extract DB names?
How do you escalate SQLi to RCE?
They want workflow — not Wikipedia answers.
🧰 Round 3 – Practical / Hands-On Lab Test
Many companies include a live technical assessment.
You may be given:
A vulnerable VM
A web application
A CTF challenge
A network lab
A cloud environment
What You’re Expected to Do
Recon & enumeration
Vulnerability discovery
Exploitation
Privilege escalation
Proof of impact
Sometimes you must also document findings.
This round answers one key question:
“Can this candidate actually hack — or just talk?”
🎭 Round 4 – Scenario-Based Discussion
This is one of the most important rounds — especially for mid-level roles.
You’ll be given hypothetical situations.
Example Scenarios
You have one IP — what’s your approach?
You find open RDP — what next?
Client blocks vulnerability disclosure — what do you do?
You detect ransomware indicators during pentest — response?
Here, interviewers assess:
Decision making
Attack chaining ability
Business awareness
Ethical responsibility
There is often no single correct answer…
…but there are wrong thought processes.
📝 Round 5 – Reporting & Documentation Evaluation
This is where many technically strong candidates fail.
Because pentesting isn’t just hacking — it’s consulting.
You must translate technical risk into business impact.
They May Ask
What sections are in a pentest report?
How do you rate vulnerability severity?
How do you explain risk to executives?
What remediation steps do you provide?
Some companies may ask you to:
Write a sample report
Fix a poorly written report
Present findings verbally
Remember:
A vulnerability that isn’t clearly reported… might as well not exist.
🧠 Final Round – Managerial / Client Round
For experienced roles, this round evaluates:
Client handling ability
Engagement planning
Team collaboration
Time estimation
Risk prioritization
You may be asked:
How do you scope a pentest?
How do you handle client conflicts?
How do you prioritize critical findings?
This round determines whether you can operate in real consulting environments.
Basic Penetration Testing Fundamentals
Before you exploit systems…
Before you launch payloads…
Before you pop shells…
Interviewers want to know one thing first:
Do you understand what penetration testing actually is?
Because penetration testing isn’t “running tools” — it’s a structured security assessment process.
If your fundamentals are weak, everything else collapses.
🔹 Question 1 – What is Penetration Testing?
How candidates answer (wrong way):
“Penetration testing is the process of finding vulnerabilities in systems.”
Too generic. Sounds memorized.
How interviewers expect you to answer:
Penetration testing is a simulated cyberattack performed in an authorized environment to identify, exploit, and demonstrate real-world security weaknesses before malicious attackers can abuse them.
Key elements to mention:
Authorized & legal engagement
Real attack simulation
Manual + automated testing
Proof of exploitation
Business risk validation
🔹 Question 2 – Vulnerability Assessment vs Penetration Testing
This is one of the most asked screening questions.
| Vulnerability Assessment | Penetration Testing |
|---|---|
| Identifies vulnerabilities | Exploits vulnerabilities |
| Tool-heavy scanning | Manual attack simulation |
| Surface-level findings | Deep exploitation |
| No proof of impact | Demonstrates real risk |
Smart interview tip:
Say this line:
“Vulnerability assessment tells you what could happen. Pentesting proves what can happen.”
🔹 Question 3 – Types of Penetration Testing
Interviewers test engagement awareness here.
Black Box Testing
No prior knowledge provided.
Simulates external attacker.
White Box Testing
Full access provided:
Source code
Architecture
Credentials
Simulates insider or deep audit.
Gray Box Testing
Partial knowledge provided.
Most common in corporate engagements.
🔹 Question 4 – What is the Pentesting Lifecycle?
This question tests methodology thinking.
A strong answer should include structured phases:
1. Reconnaissance
Gathering target intelligence.
2. Scanning & Enumeration
Identifying services, ports, users, directories.
3. Vulnerability Analysis
Mapping weaknesses.
4. Exploitation
Gaining unauthorized access.
5. Post-Exploitation
Privilege escalation, persistence, pivoting.
6. Reporting
Documenting findings & remediation.
Pro tip:
Always mention reporting — many candidates forget it.
🔹 Question 5 – What is Threat Modeling?
Threat modeling identifies:
Attack surfaces
Entry points
Trust boundaries
Threat actors
Risk impact
It helps pentesters prioritize high-value targets before testing begins.
🎯 What Interviewers Evaluate in Fundamentals
They’re checking whether you:
Understand testing scope
Follow methodology
Think legally & ethically
Know testing depth vs scanning
If you fail here…
They rarely move you to exploitation discussions.
Networking Interview Questions
If web apps are the battlefield…
Networking is the map.
Without networking knowledge, a pentester is blind.
Interviewers use networking questions to test your:
Traffic understanding
Attack feasibility awareness
Enumeration logic
Internal network exploitation ability
🔹 Question 1 – Explain the TCP 3-Way Handshake
This is foundational.
A strong answer:
SYN – Client initiates connection
SYN-ACK – Server acknowledges
ACK – Client confirms
Connection established → data transfer begins.
Why interviewers ask this:
To ensure you understand:
Port scanning logic
Firewall evasion
Packet crafting
Session establishment
🔹 Question 2 – What Happens During a Port Scan?
Good candidates explain the process, not just the definition.
Port scanning involves:
Sending packets to target ports
Observing responses
Identifying open services
Mapping attack surface
Mention scan types:
SYN scan
TCP connect scan
UDP scan
FIN scan
🔹 Question 3 – TCP Scan vs UDP Scan
| TCP Scan | UDP Scan |
|---|---|
| Connection-oriented | Connectionless |
| Faster & reliable | Slower |
| Clear responses | Often no response |
| Easier detection | Harder detection |
Interview insight:
UDP scans are crucial for discovering:
DNS
SNMP
NTP
TFTP services
🔹 Question 4 – What is ARP Poisoning?
ARP poisoning is a Man-in-the-Middle (MITM) attack where an attacker:
Sends fake ARP replies
Associates their MAC with victim IP
Intercepts traffic
Used for:
Credential sniffing
Session hijacking
Traffic manipulation
Tools example:
Ettercap
Bettercap
Arpspoof
🔹 Question 5 – How Does DNS Enumeration Work?
DNS enumeration extracts domain intelligence like:
Subdomains
Name servers
Mail servers
IP mappings
Techniques include:
Zone transfer attempts
Brute-force subdomains
Reverse DNS lookup
Tools:
DNSrecon
Amass
Sublist3r
🔹 Scenario Question – ICMP Blocked. How Will You Find Live Hosts?
Strong answers include alternative techniques:
TCP ACK ping
SYN ping
ARP ping (internal network)
Nmap host discovery flags
This tests adaptability when defenses exist.
🎯 What Interviewers Evaluate in Networking
They want to see if you understand:
Traffic behavior
Detection surfaces
Scan stealthiness
Internal attack feasibility
Because real pentests involve bypassing network controls — not just scanning websites.
Web Application Pentesting Questions
This is the highest-weightage area in most pentesting interviews.
Why?
Because web applications are:
Internet-facing
Complex
User-driven
Data-sensitive
Most corporate pentests involve web apps.
🔹 Question 1 – What is SQL Injection?
SQL Injection occurs when unsanitized user input is executed as database queries.
Example impact:
Authentication bypass
Data extraction
Database modification
Remote command execution (in some cases)
Types Interviewers Expect You to Know
Error-based SQLi
Union-based SQLi
Blind SQLi (Boolean)
Time-based SQLi
Out-of-band SQLi
🔹 Question 2 – Explain Cross-Site Scripting (XSS)
XSS allows attackers to inject malicious scripts into web pages viewed by users.
Types
Stored XSS
Payload stored in database.
Reflected XSS
Payload reflected via request.
DOM-based XSS
Client-side JavaScript manipulation.
🔹 Question 3 – What is CSRF?
Cross-Site Request Forgery tricks authenticated users into performing unintended actions.
Example:
Changing passwords
Transferring funds
Updating emails
Occurs when applications lack anti-CSRF tokens.
🔹 Question 4 – Authentication vs Authorization Flaws
Interviewers test access control logic here.
| Authentication | Authorization |
|---|---|
| Verifies identity | Verifies permissions |
| Login process | Access control |
| “Who are you?” | “What can you access?” |
Broken authorization leads to:
IDOR
Privilege escalation
Data exposure
🔹 Question 5 – What is SSRF?
Server-Side Request Forgery forces the server to make requests on behalf of the attacker.
Used to access:
Internal services
Cloud metadata
Localhost resources
High impact in cloud environments.
🔹 Practical Question – How Do You Test Login Bypass?
Interviewers want methodology:
Steps may include:
SQLi payload testing
Default credentials
Password reset abuse
JWT manipulation
OAuth misconfigurations
🔹 Practical Question – Exploiting File Upload Functionality
Strong candidates discuss:
File type bypass
Double extensions
MIME type manipulation
Web shells
RCE exploitation
🔹 Question – Tools for Web Pentesting?
Common answers:
Burp Suite
OWASP ZAP
Nikto
SQLmap
Gobuster
FFUF
But advanced candidates explain how they use them, not just list names.
🎯 What Interviewers Evaluate in Web Pentesting
They assess whether you can:
Identify attack vectors
Chain vulnerabilities
Bypass filters
Think beyond scanners
Demonstrate business impact
Because real attackers don’t stop at “XSS found.”
They escalate it to:
Account takeover
Data theft
Admin compromise
Tools-Based Interview Questions

Let’s be honest…
Tools are part of penetration testing — but over-dependence on them is one of the biggest red flags in interviews.
Any candidate can run a scanner.
But interviewers want to know:
“Do you understand what the tool is doing behind the scenes?”
Because real pentesting isn’t button-clicking — it’s controlled attack simulation.
🔹 Question 1 – How Does Nmap Work Internally?
Weak answer:
“Nmap scans ports on a target.”
Strong answer includes methodology:
Nmap sends crafted packets to target ports and analyzes responses to determine:
Open ports
Closed ports
Filtered ports
Running services
OS fingerprints
Mention techniques like:
SYN scanning
TCP connect scanning
UDP scanning
Version detection
Script scanning (NSE)
Bonus depth:
Explain how SYN scans are “half-open” and stealthier than full TCP connects.
🔹 Question 2 – Difference Between Nmap and Masscan
| Nmap | Masscan |
|---|---|
| Slower but detailed | Extremely fast |
| Service detection | Port discovery only |
| Script engine | No NSE |
| OS detection | Not supported |
Masscan is used for large-scale internet scanning…
Nmap is used for deep enumeration.
🔹 Question 3 – How Do You Use Metasploit in Engagements?
Interviewers don’t want:
“I use Metasploit to exploit vulnerabilities.”
They want workflow clarity.
A strong answer structure:
Import scan results
Search exploits
Configure payloads
Set RHOST/LHOST
Launch exploit
Gain shell
Post-exploitation modules
Bonus mention:
Meterpreter capabilities
Pivoting
Privilege escalation modules
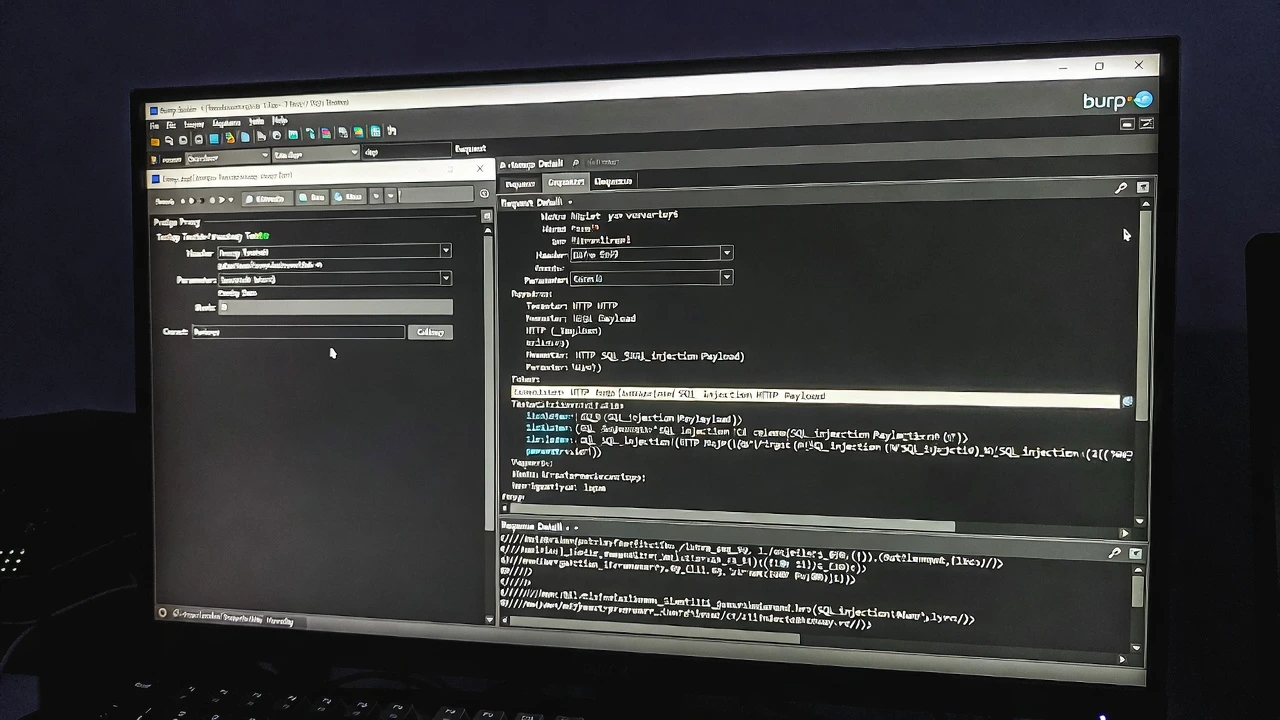
🔹 Question 4 – What is Burp Suite Proxy?
Burp Proxy acts as an interception layer between:
Client ↔ Server
It allows testers to:
Capture requests
Modify parameters
Inject payloads
Replay attacks
Test authentication flows
Interviewers love when candidates explain real usage like:
Session token analysis
Access control testing
Parameter fuzzing
🔹 Question 5 – Directory Enumeration Tools
Common tools:
Gobuster
Dirsearch
FFUF
Wfuzz
But strong candidates explain use cases:
Hidden admin panels
Backup files
API endpoints
Dev environments
🔹 Scenario – Scanner Shows Nothing. What Next?
This question tests manual testing maturity.
Good answers include:
Manual parameter testing
Business logic flaws
Authentication bypass
Client-side analysis
Source code review
Because scanners miss context-driven vulnerabilities.
🎯 What Interviewers Evaluate in Tool Discussions
They’re measuring whether you:
Understand tool output
Can validate findings
Can work manually
Know tool limitations
Avoid false positives
Because in real pentests…
Tools assist hackers — they don’t replace them.
OS & System Exploitation Questions

Now we move from web apps to operating systems.
This area tests whether you can:
Escalate access
Abuse misconfigurations
Exploit services
Maintain persistence
Because gaining initial access is only half the job…
Privilege escalation is where real pentesting begins.
🔹 Question 1 – How Do You Perform Linux Privilege Escalation?
A structured answer should include enumeration first.
Key Checks
SUID binaries
Cron jobs
Writable files
Kernel exploits
PATH misconfigurations
Capabilities
NFS shares
Tools candidates may mention:
LinPEAS
Linux Exploit Suggester
pspy
But always emphasize manual verification.
🔹 Question 2 – What is SUID Exploitation?
SUID (Set User ID) allows binaries to run with owner privileges.
If misconfigured…
Attackers can execute system commands as root.
Example:
If find has SUID → privilege escalation possible.
Interviewers expect you to mention:
GTFOBins usage
Command execution abuse
🔹 Question 3 – Windows Privilege Escalation Methods
Key techniques include:
Weak service permissions
Unquoted service paths
DLL hijacking
AlwaysInstallElevated
Token impersonation
Scheduled task abuse
Tools often mentioned:
WinPEAS
PowerUp
Seatbelt
But again — methodology matters more than tool names.
🔹 Question 4 – What is Pass-the-Hash?
Pass-the-Hash allows attackers to authenticate using NTLM hashes without cracking passwords.
Used in lateral movement.
Requirements:
Hash dump access
SMB/WinRM/RDP access
Tools:
Mimikatz
CrackMapExec
Impacket
🔹 Question 5 – Exploiting Weak Services
Interviewers test service abuse knowledge.
Examples:
Writable service binaries
Restart permissions
Misconfigured startup paths
Attackers replace binaries → gain SYSTEM access.
🎯 What Interviewers Evaluate in OS Exploitation
They want to know if you can:
Move beyond initial shells
Escalate privileges
Maintain persistence
Abuse misconfigurations
Think post-exploitation
Because real breaches escalate internally — not just externally.
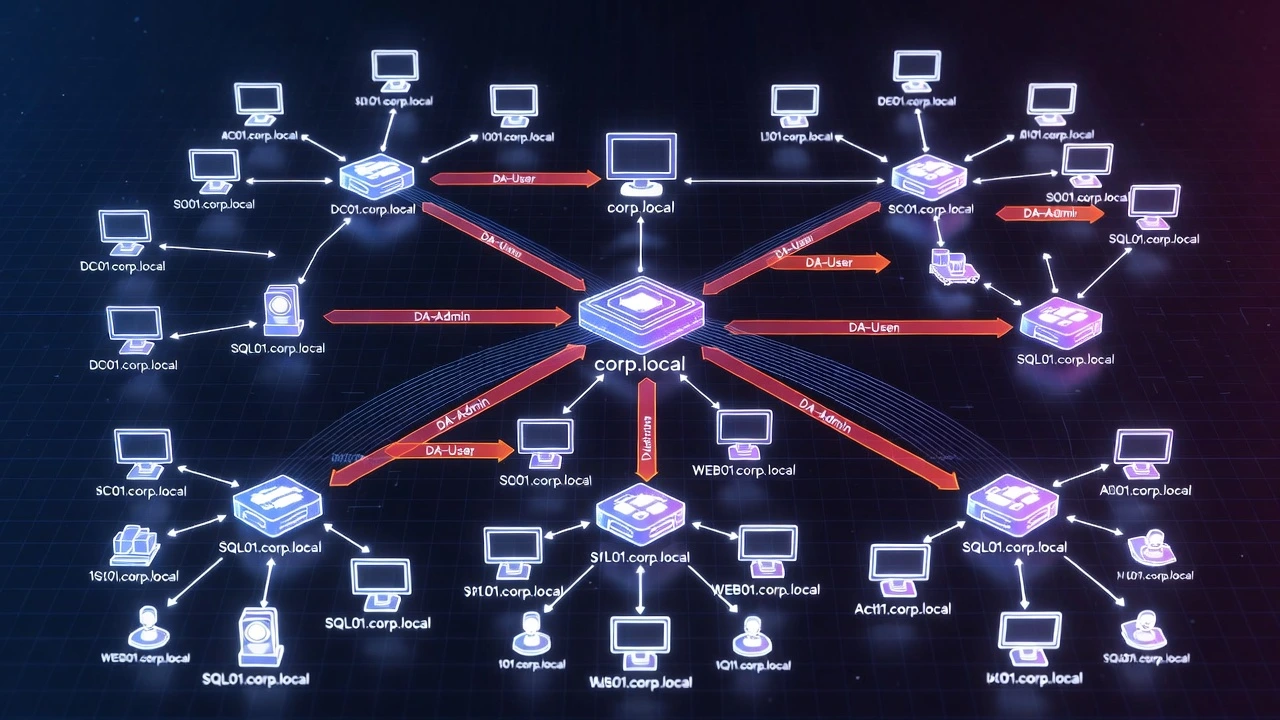
Active Directory & Internal Network Pentesting

This is where pentesting becomes enterprise-grade.
Most corporate environments run on Active Directory (AD).
So if you’re interviewing for:
Internal pentester
Red teamer
Network pentester
AD knowledge is mandatory.
🔹 Question 1 – What is Active Directory?
Active Directory is a centralized identity & access management system used in Windows domains.
It manages:
Users
Groups
Computers
Policies
Authentication
Compromising AD often means compromising the entire organization.
🔹 Question 2 – What is Kerberoasting?
Kerberoasting abuses service accounts.
Process:
Request service ticket (TGS)
Extract ticket hash
Crack offline
Retrieve service account password
Impact:
Privilege escalation
Lateral movement
Tools:
Rubeus
Impacket
Kerberoast scripts
🔹 Question 3 – What is NTLM Relay?
NTLM relay captures authentication requests and relays them to another service.
Used when:
SMB signing disabled
LDAP signing weak
HTTP relay possible
Leads to:
Unauthorized authentication
Privilege escalation
🔹 Question 4 – How Do You Enumerate Active Directory?
Strong answers include multiple techniques:
User Enumeration
LDAP queries
SMB enumeration
Kerberos pre-auth attacks
Domain Enumeration
Trust relationships
Domain controllers
Group memberships
Tools:
enum4linux
ldapsearch
CrackMapExec
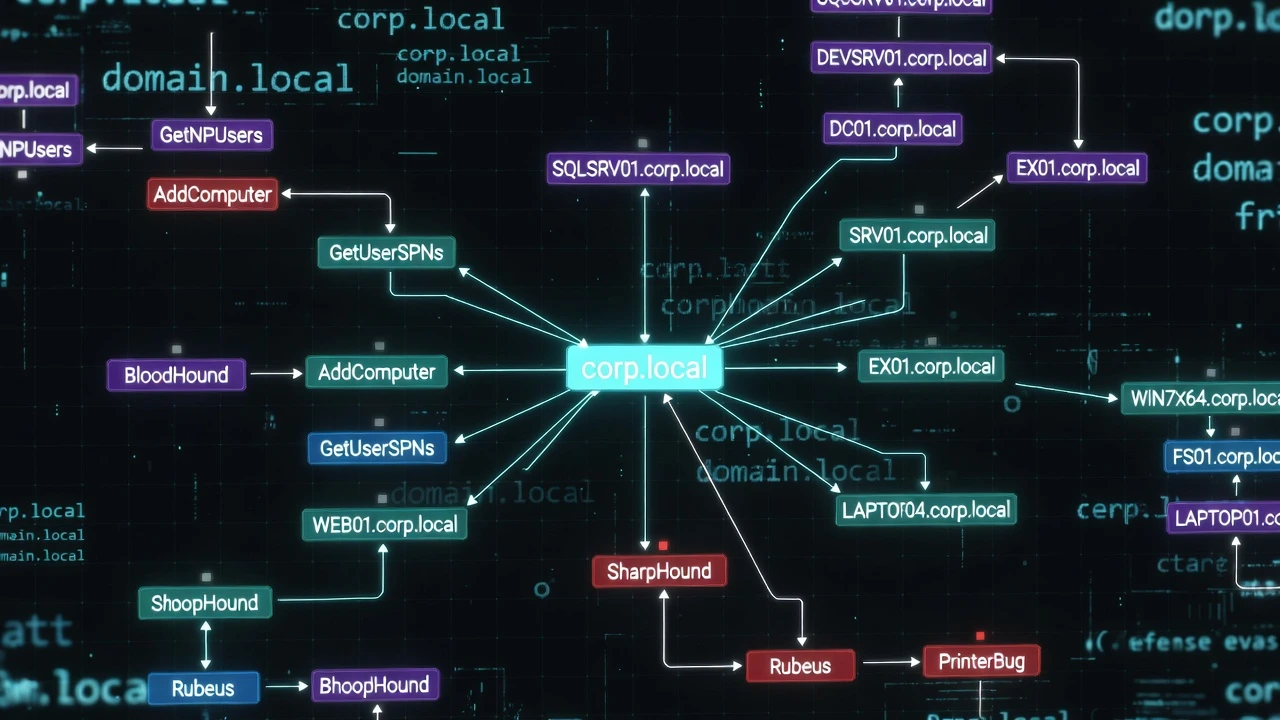
🔹 Question 5 – BloodHound Usage
BloodHound maps AD attack paths visually.
It identifies:
Privilege escalation paths
Misconfigured trusts
Admin access chains
It answers:
“How do I go from low user → Domain Admin?”
🔹 Question 6 – Lateral Movement Techniques
Interviewers love this topic.
Methods include:
Pass-the-Hash
Pass-the-Ticket
PsExec
WMI
WinRM
Shows ability to move inside networks after compromise.
🎯 What Interviewers Evaluate in AD Pentesting
They assess whether you understand:
Enterprise attack chains
Identity abuse
Privilege escalation paths
Domain dominance techniques
Because in real pentests…
Compromising one machine is a finding.
Compromising the domain is a breach.
Scenario-Based Interview Questions (Most Important)
This is where interviews shift from:
“What do you know?” → “How do you think?”
Scenario questions simulate real pentest engagements.
There’s rarely one correct answer…
…but there are definitely wrong approaches.
Interviewers evaluate:
Methodology
Creativity
Attack chaining
Decision making
Business awareness
Let’s break down some of the most commonly asked scenarios.
🔹 Scenario 1 – You’re Given One Domain & One IP. What’s Your Approach?
This is a full-scope methodology test.
A strong structured answer would look like:
Step 1 – Reconnaissance
WHOIS lookup
Subdomain enumeration
ASN mapping
Certificate transparency logs
Step 2 – Port & Service Scanning
Full port scans
Service detection
Version enumeration
Step 3 – Web Enumeration
Directory brute forcing
Parameter discovery
API mapping
Step 4 – Vulnerability Mapping
CVE correlation
Misconfigurations
Default credentials
Step 5 – Exploitation & Pivoting
Initial access
Privilege escalation
Internal enumeration
Interview tip:
Always explain the flow, not random tools.
🔹 Scenario 2 – You Find an Open SMB Share. What Next?
Interviewers want to see enumeration depth.
Strong answer path:
Anonymous login attempt
Share listing
Sensitive file discovery
Credential harvesting
Password reuse testing
Lateral movement
Bonus points if you mention:
Group policy files
Backup configs
Scripts with credentials
🔹 Scenario 3 – Web App Has File Upload Functionality
This tests exploitation creativity.
Testing approach:
File type restrictions
Double extensions (.php.jpg)
MIME type bypass
Magic byte manipulation
Web shell upload
Reverse shell execution
Then escalation:
Privilege escalation
Persistence
Pivoting internally
🔹 Scenario 4 – You Gained a Low-Privilege Shell. What Next?
This is post-exploitation thinking.
Expected methodology:
Enumeration First
User privileges
Sudo rights
Running services
Writable directories
Escalation Paths
SUID binaries
Kernel exploits
Cron jobs
Credential harvesting
Persistence
SSH keys
Scheduled tasks
Backdoor users
Interviewers want to see patience — not instant exploitation.
🔹 Scenario 5 – Firewall is Blocking Most Ports
Strong candidates discuss bypass strategies:
Full TCP scan
UDP scanning
Fragmented packets
Idle scans
Application-layer attacks
Shows understanding of network defenses.
🔹 Scenario 6 – Client Refuses to Patch Critical Vulnerability
This tests professionalism.
Good response includes:
Document risk clearly
Provide business impact
Offer remediation alternatives
Get formal risk acceptance sign-off
Shows consulting maturity — not just hacking skill.
🎯 What Interviewers Evaluate in Scenarios
They measure whether you:
Follow structured methodology
Avoid random exploitation
Think like real attackers
Consider business risk
Communicate clearly
Because real pentests are messy…
Not lab machines labeled “Exploit Me.”
Reporting & Documentation Questions
Here’s a truth many beginners don’t like:
You can be a great hacker…
…and still fail as a pentester if you can’t write reports.
Because companies don’t pay for exploits.
They pay for risk visibility.
If stakeholders don’t understand your findings…
Your work has no business value.
🔹 Question 1 – What Should a Pentest Report Include?
A professional report usually contains:
1. Executive Summary
Non-technical overview
Business impact
Overall risk posture
2. Scope & Methodology
Assets tested
Testing approach
Limitations
3. Findings Summary
Vulnerability list
Severity ratings
4. Technical Details
For each vulnerability:
Description
Affected assets
Steps to reproduce
Proof of Concept
Screenshots
5. Risk Impact
Data exposure
Financial damage
Operational risk
6. Remediation Steps
Fix recommendations
Security controls
🔹 Question 2 – How Do You Calculate CVSS Score?
CVSS (Common Vulnerability Scoring System) measures severity based on:
Attack vector
Complexity
Privileges required
User interaction
Impact on CIA triad
(CIA = Confidentiality, Integrity, Availability)
Interviewers want you to understand risk ranking — not memorize numbers.
🔹 Question 3 – How Do You Explain Risk to Non-Technical Clients?
This tests communication maturity.
Weak answer:
“I explain the vulnerability.”
Strong answer:
Translate technical risk into business impact.
Example:
Instead of saying:
“SQL Injection allows database access.”
Say:
“An attacker could extract customer data, leading to regulatory fines and brand damage.”
Executives understand risk — not payloads.
🔹 Question 4 – Difference Between Vulnerability & Risk
| Vulnerability | Risk |
|---|---|
| Security weakness | Business impact |
| Technical flaw | Exploitable consequence |
| Example: XSS | Example: Session theft |
A system may have vulnerabilities…
…but risk depends on exploitability + impact.
🔹 Question 5 – What Makes a Good Pentest Report?
Interviewers expect you to mention:
Clarity
Reproducibility
Evidence-backed findings
Business impact explanation
Actionable remediation
Bonus points:
Mention screenshots, request/response logs, payload samples.
🔹 Practical Reporting Test (Some Interviews)
You may be asked to:
Write a sample finding
Fix poor documentation
Rate vulnerability severity
Present findings verbally
Because client communication is part of the job.
🎯 What Interviewers Evaluate in Reporting Skills
They assess whether you can:
Communicate with executives
Translate tech → business risk
Write structured findings
Provide remediation
Maintain professionalism
Because pentesters are not just attackers…
They are security consultants.
HR & Behavioral Interview Questions for Pentesters
Most candidates relax when they hear:
“This round is just HR.”
That’s a mistake.
Because HR rounds in cybersecurity hiring are not just about culture fit — they evaluate:
Passion for ethical hacking
Ethical maturity
Real-world exposure
Learning mindset
Communication ability
Remember…
Companies are hiring someone who will be legally authorized to hack systems.
So trust, ethics, and professionalism matter as much as technical skill.
🔹 Question 1 – Why Do You Want to Become a Penetration Tester?
This is almost guaranteed to be asked.
Weak answers:
“I like hacking.”
“It’s interesting.”
“Good salary.”
Strong answer structure:
Interest origin story
Learning journey
Practical exposure
Career vision
Example flow:
“My interest started when I learned how real attackers exploit systems. I began practicing on labs like vulnerable VMs and web apps, documented my findings, and developed a structured testing methodology. I enjoy offensive security because it combines technical depth with real business impact.”
This shows seriousness — not hype.
🔹 Question 2 – Describe Your Most Challenging Pentest / Lab
Interviewers want storytelling here.
Structure your answer like:
Target/lab type
Initial difficulty
Enumeration process
Exploitation path
Escalation method
Key learning
They’re testing:
Problem-solving ability
Persistence
Methodology
Not just whether you solved it.
🔹 Question 3 – Do You Have Bug Bounty or Real-World Experience?
If yes:
Explain vulnerability found
Impact
Disclosure process
Remediation outcome
If no:
Talk about:
Lab writeups
CTFs
Simulated pentests
Portfolio reports
Companies value proof of practice — not just certificates.
🔹 Question 4 – How Do You Stay Updated in Cybersecurity?
Strong candidates mention:
Security blogs
Research papers
CVE databases
Exploit releases
Conference talks
Labs & simulations
This shows continuous learning — critical in offensive security.
🔹 Question 5 – What Would You Do If You Accidentally Caused Downtime?
This tests ethical and professional responsibility.
Expected response includes:
Immediately stop testing
Inform client/stakeholders
Document incident
Assist recovery if needed
Shows maturity and accountability.
🔹 Question 6 – Have You Ever Found a Vulnerability Without Permission?
This tests ethics.
Correct approach:
Do not exploit further
Report responsibly
Follow disclosure guidelines
Any reckless answer is a red flag.
🎯 What HR Evaluates in Pentesters
They’re assessing whether you are:
Ethical
Trustworthy
Professional
Communicative
Passion-driven
Because pentesters operate with legal attack authorization.
Trust is non-negotiable.
Penetration Testing Interview Preparation Roadmap
Now comes the most actionable part of the blog.
Because knowing questions is not enough…
You need a structured preparation path.
Let’s break it down from beginner → job-ready pentester.
🧭 Phase 1 – Build Strong Foundations
Start with core IT fundamentals.
Focus Areas
Networking basics (TCP/IP, DNS, routing)
Operating systems (Linux + Windows)
Web architecture
HTTP/HTTPS protocols
Firewalls & proxies
Without foundations, exploitation becomes guesswork.
🧪 Phase 2 – Learn Pentesting Methodology
Before tools — learn process.
Understand:
Reconnaissance
Scanning
Enumeration
Exploitation
Post-exploitation
Reporting
Practice explaining this flow verbally — interviews love methodology clarity.
🌐 Phase 3 – Web Application Security
This is the highest hiring demand area.
Master vulnerabilities like:
SQL Injection
XSS
CSRF
IDOR
SSRF
File upload flaws
Practice on:
Vulnerable labs
Practice platforms
Realistic web apps
Focus on manual testing — not just scanners.
🖥️ Phase 4 – System Exploitation & Privilege Escalation
Move beyond web apps into host compromise.
Learn:
Linux privilege escalation
Windows privilege escalation
SUID abuse
Service exploitation
Credential dumping
Practice post-exploitation workflows.
🏢 Phase 5 – Active Directory Attacks
For corporate pentest roles, AD is critical.
Focus on:
Domain enumeration
Kerberoasting
NTLM relay
Pass-the-Hash
BloodHound attack paths
This separates junior from mid-level pentesters.
🧰 Phase 6 – Tool Mastery (With Depth)
Learn tools — but also their internals.
Key tool stack:
Nmap
Burp Suite
Metasploit
Gobuster / FFUF
CrackMapExec
Impacket
Practice manual validation of tool findings.
📝 Phase 7 – Reporting & Documentation Practice
Most candidates ignore this — big mistake.
Practice writing:
Vulnerability reports
Executive summaries
Risk impact statements
Remediation guidance
Build a pentest report portfolio.
🎯 Phase 8 – Build a Public Pentest Portfolio
Show proof of skill.
Portfolio ideas:
Lab writeups
GitHub reports
Exploit PoCs
Methodology breakdowns
Bug bounty disclosures
This builds recruiter trust instantly.
⏳ Suggested 6-Month Preparation Timeline
Months 1–2
Networking + Linux + Web basics
Months 3–4
Web exploitation + Labs
Month 5
Privilege escalation + AD basics
Month 6
Full pentest simulations + Reporting
🎯 Interview Readiness Checklist
You’re ready when you can:
Explain methodology without notes
Perform enumeration confidently
Escalate privileges in labs
Write structured reports
Solve scenario questions logically
If yes — start applying.
Certifications That Help in Penetration Testing Interviews
Let’s clear a common myth first:
Certifications alone won’t get you hired… but they can open interview doors.
Recruiters use certifications as filters, not final decision factors.
Your practical skills, labs, and methodology thinking still matter more.
Here are the certifications that actually carry interview weight:
🔹 Beginner Level Certifications
Best for foundational credibility:
eJPT – Practical beginner pentesting
Security+ – Security fundamentals
CEH – HR recognition (theory-heavy)
These help freshers pass resume screening.
🔹 Intermediate Level Certifications
Valued for hands-on testing skills:
PNPT – Real-world pentest methodology
eCPPT – Practical exploitation focus
CRTP – Active Directory specialization
These certifications show job readiness.
🔹 Advanced / Elite Certifications
Highly respected in offensive security:
OSCP – Industry gold standard
OSEP / OSED – Advanced exploitation
CRTO – Red teaming operations
Interviewers often assume OSCP holders understand:
Enumeration depth
Privilege escalation
Attack chaining
🎯 Certification Strategy Tip
Don’t chase too many certs.
A stronger path is:
Labs + Portfolio + 1 Practical Certification > 5 Theory Certifications
Common Mistakes Candidates Make in Pentest Interviews
After interviewing hundreds of candidates, recruiters see repeating patterns.
Avoid these — they cost people jobs.
❌ Mistake 1 – Tool Dependency
Candidates say:
“I run Burp scan.”
“I run Nessus.”
But can’t explain manual testing.
Tools assist pentesters — they don’t replace thinking.
❌ Mistake 2 – Weak Networking Knowledge
Many candidates jump into web hacking…
…but fail basic questions like:
TCP handshake
Port scanning logic
Firewall evasion
This signals shallow foundations.
❌ Mistake 3 – No Methodology Explanation
Saying:
“I try exploits.”
Is not methodology.
Interviewers expect structured flows:
Recon → Enum → Exploit → Escalate → Report
❌ Mistake 4 – Ignoring Post-Exploitation
Getting a shell isn’t the goal.
Real pentesting includes:
Privilege escalation
Credential harvesting
Lateral movement
Stopping at initial access shows inexperience.
❌ Mistake 5 – Poor Reporting Skills
Some candidates exploit complex systems…
…but can’t write a vulnerability report.
Remember:
If you can’t communicate risk, the exploit has no business value.
Pro Tips to Crack Penetration Testing Interviews
Let’s end the preparation with recruiter-level insider advice.
🔥 Tip 1 – Think Aloud While Answering
Interviewers don’t just want answers…
They want your thought process.
Explain:
Why you test something
What you expect to find
What you’ll do next
🔥 Tip 2 – Use Real Lab Examples
Whenever possible, say:
“In one lab, I exploited…”
This proves hands-on exposure instantly.
🔥 Tip 3 – Draw Attack Paths
If it’s a whiteboard interview:
Map network flow
Show trust relationships
Explain pivoting visually
Visual thinkers stand out.
🔥 Tip 4 – Build a Pentest Portfolio
Have proof ready:
GitHub writeups
Lab reports
Exploit demos
Methodology docs
Portfolios often outweigh resumes.
🔥 Tip 5 – Don’t Fake Knowledge
If you don’t know something:
Say:
“I haven’t exploited this yet, but my approach would be…”
Honesty + logical thinking > bluffing.
🧠 Rapid-Fire Pentest Interview Questions (Bonus)
Here’s a quick revision list before interviews:
What is IDOR?
What is LFI vs RFI?
What is SSRF?
What is reverse shell?
What is pivoting?
What is banner grabbing?
What is NTLM relay?
What is Kerberoasting?
What is CVSS?
What is pass-the-hash?
Use these for last-minute prep.
🏁 Conclusion – From Learner to Hired Pentester
Breaking into penetration testing isn’t easy…
…but it’s absolutely achievable with the right preparation strategy.
Remember:
Interviews test thinking — not memorization
Methodology matters more than tools
Reporting matters as much as exploitation
Ethics matter as much as skill
Anyone can learn payloads…
But companies hire pentesters who can:
Think like attackers
Act responsibly
Communicate risk clearly
Simulate real breaches
So focus on:
Labs
Realistic scenarios
Attack chains
Documentation
Continuous learning
Because at the end of the day:
Companies don’t hire hackers who know tools…
They hire hackers who understand attack logic.

